Our electronic lives have over the years become a veritable treasure trove of digital information. An increase in smartphone usage has led to a growing addiction to apps, in particular, social media apps, that have made us visible to the naked eye online, whether we chose to do so or not.
The collation, bulk collection of the metadata that is gathered whenever we go online, is analogous to a violation of our right to privacy, as defined and endorsed by leading human rights organisations, including the UN Special Rapporteur on freedom of expression, the UN Special Rapporteur on counter-terrorism and the High Commissioner for human rights.
The information being collected by telecom companies, for example, includes our personal details having our address, telephone numbers and our NIC, biometric identification at their disposal.
Due to the lack of a Data Protection Act, we can neither sue the companies for any breach of data that occurs and how can they be held liable? Which then leads to the question how these companies are protecting our data, because confidential information is at risk of being leaked out. Is the data being stored on their servers, encrypted in any given way?
Without prior user consent, data should not be shared with third parties. The aim of a Data Protection Act is to create a balance between the rights of individuals and competing interests of those with legitimate reasons for using personal information.
The fast pace at which technology is innovating, advancing and accelerating, the data protection policies and guidelines are failing to keep up to date.
As Pakistan makes the foray into the digital age, with a growing percentage of work being done online, from banking, marketing, and management to technology outsourcing; we have no law to address data protection and privacy. The issue being faced worldwide with data protection & privacy laws are their in-adeptness to protect individuals from the privacy implications that upcoming technologies present.
In the absence of any official data protection act in Pakistan, ISPs and any companies that house our personal data on their servers and systems are bound to cave into the measures proposed by the cybercrime bill, due to the legal ramifications.
With a lack of access to protection measures by individuals, and a lack of judicial oversight, what are the options left that can be exercised by organisations and individuals?
Data retention by ISPs can be utilized by regulatory authorities to keep track of political dissidents and critics of the government, allowing them to be under threat from proverbial assaults, including blackmail.
It also raises the possibility of breaches of confidentiality between journalists and their sources – a concern that becomes a central matter of discussion abroad, in the wake of the whistle-blowing activities of Edward Snowden.
To continue to legally operate, ISPs in Pakistan must comply with these data retention measures as laid out by the cyber-crime bill, for their own survival. In doing so, furthermore, a dangerous precedent is set, wherein ISPs have no choice but to monitor and store the digital movements of their customers and users.
Factoring the massive data leak reported by Careem in which data of over 14 million users was compromised, begs the question as to why a data protection act hasn’t been promulgated.
The absence of a data protection act leaves users with no leverage over the legal options they could exercise, as they are left at the mercy of companies and unable to know the extent of the breach for e.g. in case of Careem.
The disclosure of the hacking was made public three months after its discovery and can be termed as appalling.
However, Careem is lucky it can’t be reined in by the absence of any appropriate law and stands vindicated in its stance that it reported about the breach and issued an apology with instructions on how to change passwords.
And the data which was leaked begs the question, were the user details encrypted by the company? What measures did Careem take to protect their user database?
Digital Rights Foundation in a published statement regarding the Careem hack and disclosure said “This particular breach of Careem’s security protocols raises a lot of queries and concerns that their statement failed to answer. First and foremost, why did it take four months to report the incident to the public? Although the blog states that they took their time to investigate into the details of the breach due to the complex nature of the incident, but the fact remains – millions of Careem’s customers and drivers were using their compromised accounts while their data was compromised. Customers were kept in the dark and had no mechanism of holding the company accountable.
Secondly, the statement fails to mention the number of customers that were affected by this breach. Careem is used by over 14 million users around the world, and the silence of this important aspect could signify that all of the users were influenced.”
How Twitter responded to a glitch in their system
Last week, Twitter in a blog post and series of tweets disclosed that a glitch in their systems resulted in passwords being stored in readable form on its internal computer system instead of being masked by a technique known as hashing.
It immediately asked all its 330 million users to reset their passwords, although an internal investigation conducted by the company revealed no passwords were stolen or misused.
As per media reports, Twitter acted swiftly after discovering the bug three weeks ago and is said to have reported it to regulators.
Although, both cases draw interesting parallels. Careem’s disclosure came three months after its discovery compared to Twitter, where it took less than three weeks to come out publicly with it.
Also, Twitter served a full-screen alert to users upon login, told them as to what happened and offered instructions on how to change their passwords and strongly recommended to do it.
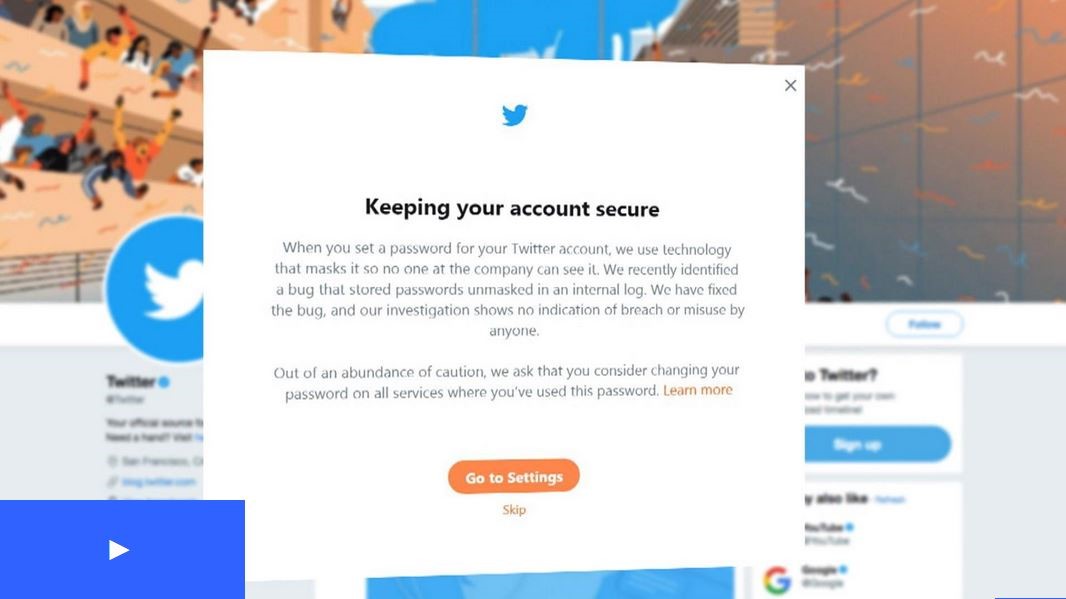
The transparency on part of Twitter and the timely disclosure is commendable when compared to Careem where it didn’t bother to apprise customers within its app that a hack had taken place and recommend them to immediately change their passwords.
The sophistication of hackings and online data leakages is never-ending, but Careem’s veiled secrecy over this massive leak of user data and lack of user awareness raises chilling questions about the primacy that we attach to data protection and privacy.
Companies will keep on evading their responsibilities in absence of laws pertaining to data protection, as they won’t be taken to task for such leaks and mere disclosures would absolve them of all their responsibilities.
The relevant authorities need to set their priorities right and ensure that a data protection legislation is enacted to provide consumers with appropriate protection and options available to seek legal recourse in case of serious data breaches.